Whether You Build Them or Buy Them – IoT Device Security Concerns Us All

The Internet of Things (IoT) offers many attractions for small and medium-sized manufacturers (SMMs) who may want to integrate IoT into their facilities and operations, or who seek to enter the IoT market with innovative products. The spectrum of available IoT products is broad and continually growing. When venturing into the IoT waters, it’s helpful to be prepared for the potential cybersecurity pitfalls, whether in the form of implications for organizational risk management when introducing IoT to the environment or considerations for product design and support when entering the marketplace as a product vendor. The NIST Cybersecurity for the Internet of Things program is working to provide the information that SMMs need to navigate these potentially turbulent waters.
IoT and Risk Management
Before you install smart thermostats to keep your employees comfortable, add smart coffee pots to break rooms to keep them caffeinated or deploy the latest and greatest Industrial Control System (ICS) technology in your production environment, it’s important to recognize the potential implications. You may have a robust information security program for your traditional IT, but those tools, processes and procedures will likely require adaptation when IoT is introduced. Some of the ways that IoT is different include:
- Interacting with the physical world. IoT devices are equipped either with sensors that collect information from their environment or actuators that cause “real world” objects to move or change. Sensing can generate a lot of potentially sensitive data, so knowing what is collected and where it’s going is important. A compromised actuator could enable an adversary to cause significant disruption – think what could happen if you don’t know who is commanding your smart locks.
- Challenging conventional IT management practices. IoT devices are often “black boxes” that both obscure their internal goings-on and can’t be equipped with agents or queried in the same manner as servers, desktops or firewalls. As a result, common IT management practices can prove ineffective with IoT. These management challenges can multiply quickly if you’re deploying IoT devices “at scale.”
- Lacking common cybersecurity and privacy features. IoT devices often lack support for logging and monitoring, support for updating devices to address newly identified vulnerabilities, or cryptographic capabilities needed to protect sensitive information they generate or process. It cannot be assumed these devices possess the same cybersecurity capabilities as IT devices on the same network.
SMMs adopting IoT into their environments need to be prepared to address these challenges. If entering the IoT market as a vendor, understanding these challenges can be an opportunity to develop a product that provides a better customer experience.
Managing Your IoT Security Risk
When adopting IoT technology in your organization, SMMs should plan to address these challenges with an eye toward three goals:
- Protecting IoT device security to ensure that the product is fully under the owner’s control, and not being exploited by outside actors to gain access to the SMM’s network or participate in a botnet.
- Protecting data security so that data generated by IoT devices isn’t exposed or altered while stored on the devices, transferred across the network or transmitted to a cloud-based service used to provide aspects of the product’s capabilities.
- Protecting individuals’ privacy, being alert to the possibility of privacy-sensitive information being captured or created by IoT products, and cognizant of where that data might travel.
These goals are articulated in NISTIR 8228, Considerations for Managing Internet of Things (IoT) Cybersecurity and Privacy Risks, and can be difficult to achieve with currently available IoT products. For organizations that are applying the NIST Cybersecurity Framework (CSF) or defining their security requirements using NIST SP 800‑53 controls, NISTIR 8228 identifies a range of challenges that IoT devices present to achieving the ends that the CSF and SP 800‑53 intend. For example, control SI-2, Flaw Remediation, from SP 800‑53 cannot be satisfied by IoT devices that lack an ability for secure software/firmware updates. Similarly, many IoT devices cannot be analyzed in a manner needed to satisfy the CSF subcategory DE.CM-8: Vulnerability scans that are performed.
Consideration for the three goals identified above should factor into the selection of IoT products as well as how they are managed, as the security capabilities of IoT devices contribute to achieving the overall security requirements of the systems into which the devices are integrated.
Improving Your IoT Products’ Security Posture
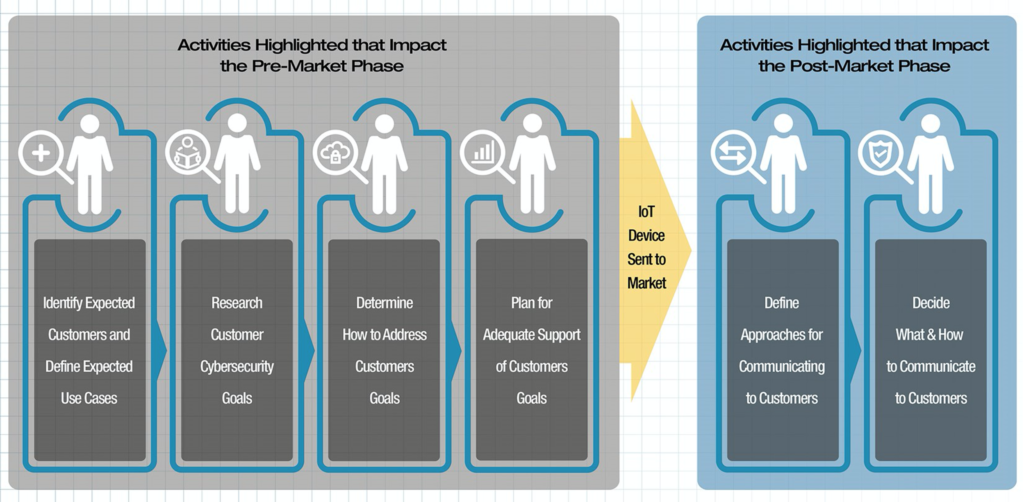
If you are venturing into the creation of IoT products, awareness of cybersecurity challenges can help guide your approach to the development and support of your product. The three goals described above also apply when developing an IoT product. A thoughtful approach to development with those goals in mind will result in a more manageable, more secure product. This approach involves both the design and development phase for the product and the support phase once it’s brought to market, as illustrated in this figure from NISTIR 8259, Foundational Cybersecurity Activities for IoT Device Manufacturers.
Technical Cybersecurity Capabilities
| Device Identification | The IoT device can be uniquely identified logically and physically. |
| Device Configuration | The configuration of the IoT device’s software can be changed, and such changes can be performed by authorized entities only. |
| Data Protection | The IoT device can protect the data it stores and transmits from unauthorized access and modification. |
| Logical Access to Interfaces | The IoT device can restrict logical access to its local and network interfaces, and the protocols and services used by those interfaces, to authorized entities only. |
| Software Update | The IoT device’s software can be updated by authorized entities only using a secure and configurable mechanism. |
| Cybersecurity State Awareness | The IoT device can report on its cybersecurity state and make that information accessible to authorized entities only. |
Non-Technical Supporting Capabilities
| Documentation | The ability for the manufacturer and/or supporting entity to create, gather and store information relevant to cybersecurity of the IoT device throughout the development of a device and its subsequent lifecycle. |
| Information and Query Reception | The ability for the manufacturer and/or supporting entity to receive from the customer information and queries related to cybersecurity of the IoT device. |
| Information Dissemination | The ability for the manufacturer and/or supporting entity to broadcast and distribute information related to cybersecurity of the IoT device. |
| Education and Awareness | The ability for the manufacturer and/or supporting entity to create awareness of and educate customers about elements such as cybersecurity-related information, considerations and features of the IoT device. |
The planning activities combined with applying the technical and non-technical baselines will help SMMs develop products that are both more secure-able and better supported, helping your customers to take advantage of your IoT innovations while limiting the impact to their risk management challenges.
This article originally appeared on NIST’s Manufacturing Innovation blog and is reprinted with permission.
